
Corporate Hacking: Are You a Target? - IEEE Innovation at Work
4.6
(781)
Écrire un avis
Plus
€ 24.50
En Stock
Description
5 strategies that companies and organizations can use to protect their networks from corporate hacking and defend against cyber attack.
Gamification presentation for ieee 2013 03
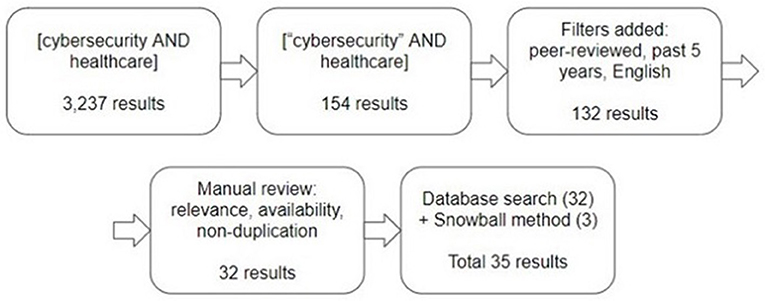
Frontiers Hospital cybersecurity risks and gaps: Review (for the

Assessment 2 -Unethical human activity is primarily responsible

Hackathon and Society. Hacks for Humanity : 36-hour…
The Ungoverned Space of US Space-Cyber Governance - Centre for

Hacker - Wikipedia

What Is Adaptive Authentication?

Computer security - Wikipedia

The Impact of AI on Cybersecurity

Hackers could try to take over a military aircraft; can a cyber
Tu pourrais aussi aimer









